Getting started
Get started with Apono in 10 minutes to get dynamic, centralized, just-in-time access management for your cloud!
Getting started
Get a taste of what Apono can do by signing up (it's free!) and then follow our onboarding wizard.
You will complete 3 steps to see how easy it is for Admins to manage access with dynamic Access Flows, and how intuitive it is for developers and other end users to request and use Apono access just-in-time.
Try Apono in AWS, then unlock all of your cloud providers and applications for centralized, streamlined access management.
Step 1
Install the connector
What's a connector? What makes it so secure?
The Apono Connector is an on-prem connection that can be used to connect resources to Apono and separate the Apono app from the environment for maximal security.
Read more here.
If you're just getting started with Apono, we recommend using a local connector deployed with docker image.
You can also install a connector in your cloud environment. Read more here.
You should know:
A local connector is only active as long as the container is running. This means you will have to rerun the command when the container is down.
The local connector leverages your existing AWS Profiles. Make sure you have an AWS Profile with Admin permissions to an AWS account, like playground, staging, dev, etc.
If your organization requires MFA, SSO login, VPN login or other security policies, the local connector using your AWS profile will need them to work.
How to deploy the local connector
Prerequisites
A configured AWS profile in your AWS CLI with these permissions: List and IAM to the AWS account and resources you want to integrate.
Steps
Go to the Apono app and sign up
In the catalog, pick AWS.
Pick Account
Install a new connector and pick "Local Installation"
For Linux/mac:
Copy the command that appears in the Apono App and run it in your terminal:
bash <(curl -s https://apono-public.s3.amazonaws.com/local-connector/install.sh) --apono-token <TOKEN>The<TOKEN>will appear in the one-liner the UI generates for you.Follow the interactive prompts and assign:
AWS profile: Apono will leverage the permissions of the profile you pick. If you don't specify the profile, press enter and Apono will use the default profile.
Results:
If installed successfully, you will see this message: Installation complete. You can return to the Apono App
Go back to the Apono App and continue to integrate AWS. The local connector should appear on the screen with a green checkmark:

For Windows
Copy the command that appears in the Apono App and run it in your terminal:
iex ([System.Text.Encoding]::UTF8.GetString((Invoke-WebRequest -Uri "https://apono-public.s3.amazonaws.com/local-connector/install.ps1" -UseBasicParsing).Content))Follow the interactive prompts and assign:
The
<APONO TOKEN>that appears in the Apono App under the one-liner command.
Results:
If installed successfully, you will see the container ID that started running.
Go back to the Apono App and continue to integrate AWS. The local connector should appear on the screen with a green checkmark:
Integrate AWS with Apono
Provide the AWS config:
An integration name of your choosing
The region of the account you'd like to integrate
Click Connect
Wait for the integration to sync. This may take a few minutes.
Results:
You should see a success message indicating that Apono has successfully integrated with AWS Test.
Otherwise, go back and edit the integration to fix the errors that appear on the screen. Learn more here.
Step 2
Create an Access Flow
An Access Flow is a smart, dynamic access workflow or policy in human readable language that determines who can request access to what, and what the access duration and approval flow should be. Read more about Access Flows here.
Fill in the Access Flow form:
Click Someone to pick who can request the access. You can pick yourself under Users.
Click Select Target to pick the AWS Account you just connected and the cloud service you'd like to manage access to. Duplicate this line to include more cloud services in the Access Flow.
Click Any to pick the specific resources in the Access Flow by name, by AWS tags, or by excluding specific resources. You can also leave it as Any.
Click Permissions to pick the permissions users will be able to request.
You can leave the access time as 1 Hour and the approval as Automatic or change them as you'd like.
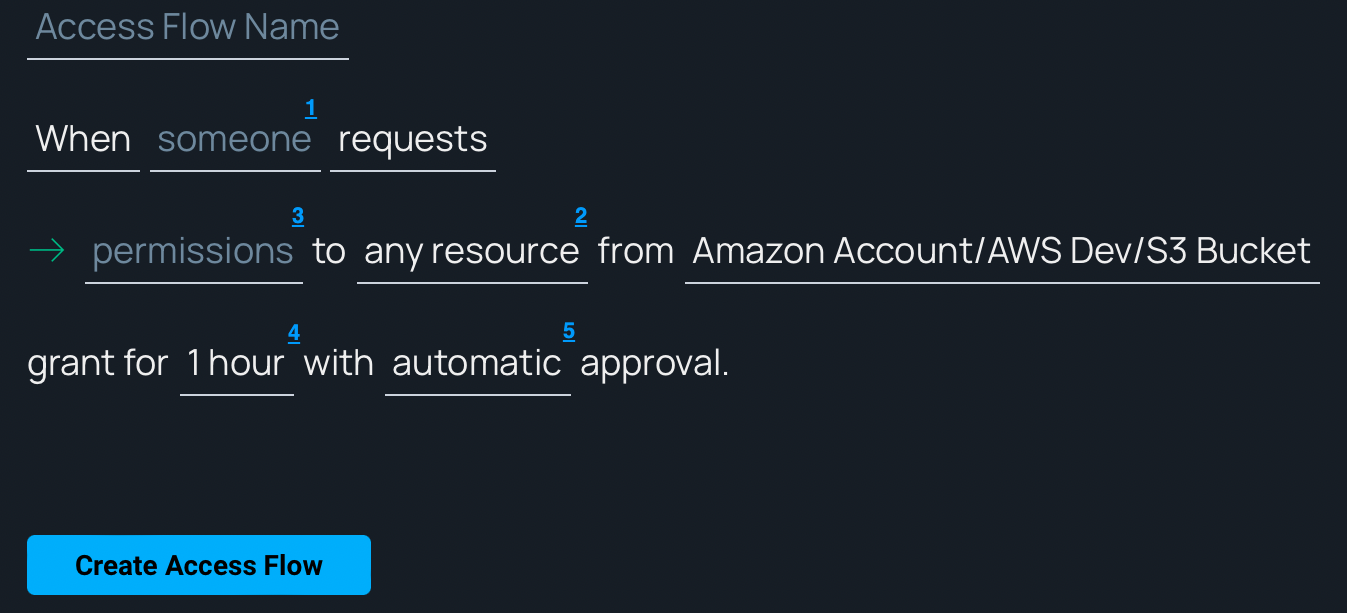
Click Create Access Flow.
In the next screen, click Request Access continue to Step 3.
Step 3
Request access
Developers and other end users in the organizations will request access according to the Access Flows using Slack, Teams, CLI, or the Apono Web Portal.
Fill in the request form:
Pick the integration
Pick the resource type
Pick resources
Pick permissions
Insert a justification

Click Request
Gain and use access
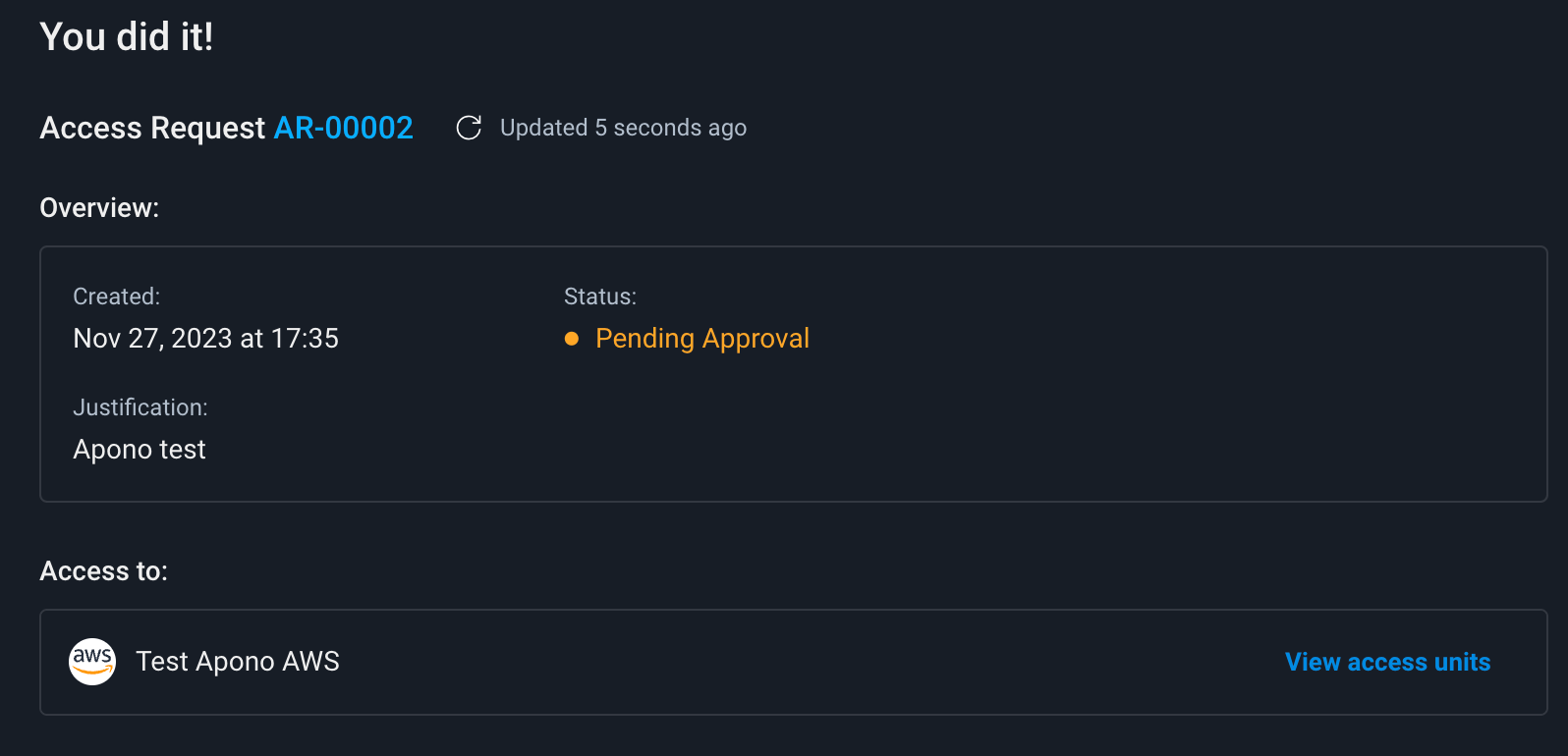
The request will appear on the screen with the status Pending
Once the connector provisions the access successfully, the status of the request will change to Granted
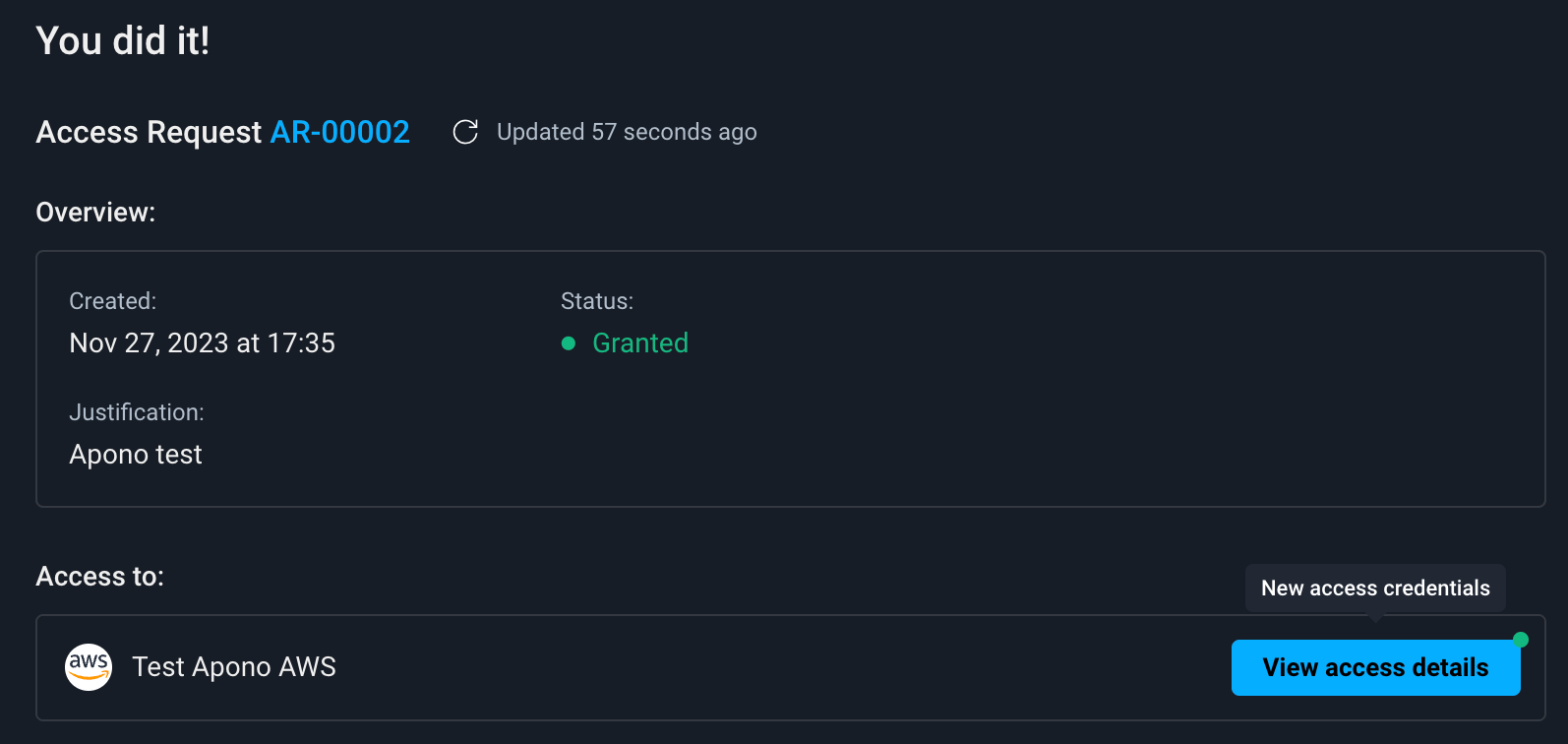
Click View access details
The access details can be used to gain the access you just requested! Test it in AWS!
Click Finish onboarding.
All done!
Check out the Apono Activity log to see how Apono reports and audits access requests.
You can also Revoke the access you were just granted to see how Apono deprovisions access when the access time is up.
Last updated
Was this helpful?
