# Production Stability and Management
## Intro
Downtime is one of the scariest words in product development. When customers and users trust your product, they expect performance, quality and availability, often governed by [Service Level Agreements (SLA)](/docs/access-flows/common-use-cases/ensuring-sla.md).
Apono helps admins and resource owners control access to their production assets with dynamic Access Flows.
* Just-in-Time access requests keep your production environments least-privilege, which prevents human errors and sabotage.
* When needed (for everyday work or during incidents), developers can be granted temporary access.
* Access requests help prevent errors and confusion with pre-defined bundles for incidents and tasks.
## How to improve production stability with Apono
### Access bundles for tasks or incidents in production
With Apono, users can request bundles set for different tasks and incidents by admins or create freeform access requests based on their Access Flows. The process prevents users logging in to the wrong environment or tenant and performing changes.
1. Integrate your cloud environments with Apono
2. Integrate other crucial production systems, like CI/CD tools, databases and you incident response tool
3. Create an access bundle containing exactly the right resources and permissions for different incidents, production environments, customers and teams.
4. When needed, developers can use Slack, Teams or CLI to request that bundle temporarily
This process limits the access users can request and helps them focus; when there's an urgent production incident, developers can request all the access with a single click.
### Least privilege and access control in production
Keeping production environments least privilege in the first place reduces risk of downtime; the less users can perform CRUD actions on your sensitive assets, the last issues and errors you'll run into.
With Apono, you can:
1. Integrate your cloud environments and other crucial production systems, like CI/CD tools databases with Apono
2. Use tags to label your most sensitive instances and resources
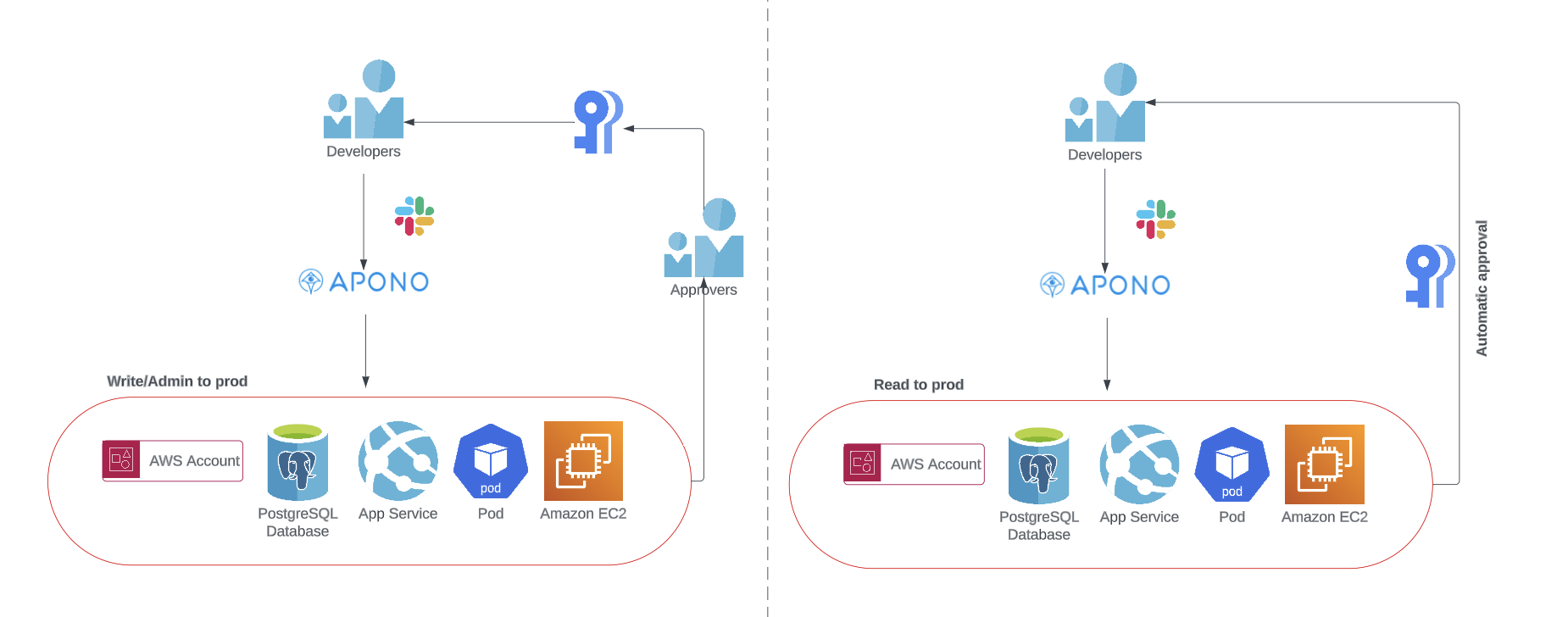
3. Create Access Flows around production instances and resources with differing flows;
1. Read access can be granted temporarily and automatically
2. Write access can be granted temporarily with approval
3. Delete and Admin access can be granted temporarily with several approvers
4. Approvers can be a developers' team lead, the resource owner, your DevOps, DevSecOps, Infra or other team, as well as shift members. Apono also lets you require several approvers for extra-sensitive actions and resources.
5. When needed, developers can use Slack, Teams or CLI to request access to production
### Separation of environments and tenants
As your product and company grow, more and more environments, tenants and accounts are created. Each developer has several local and staging/development/playground environments at any given moment, on top of different environments or tenants for customers.
This naturally causes confusion and, unfortunately, human errors in production. Developers are accessing the wrong environment, deploying code to production by accident and moving, changing or even deleting databases.
Apono helps prevent unnecessary production incidents:
1. Admins separate environments with bundles and Access Flows, making their management easier
2. Admins control what resources are requestable for different users, so that users can only request access relevant to them
3. Users create access requests and pick bundles or resources they need access to. When approved, access details are sent with the link to the exact instance, preventing confusion
4. If you decide to require approvers, another user will examine the request to make sure the resources and permissions make sense for that user.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://docs.apono.io/docs/access-flows/common-use-cases/production-stability-and-management.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.