# Revoke Access
A big, often overlooked, part of access management is revoking access; de-provisioning access, removing group membership and deleting orphaned accounts.
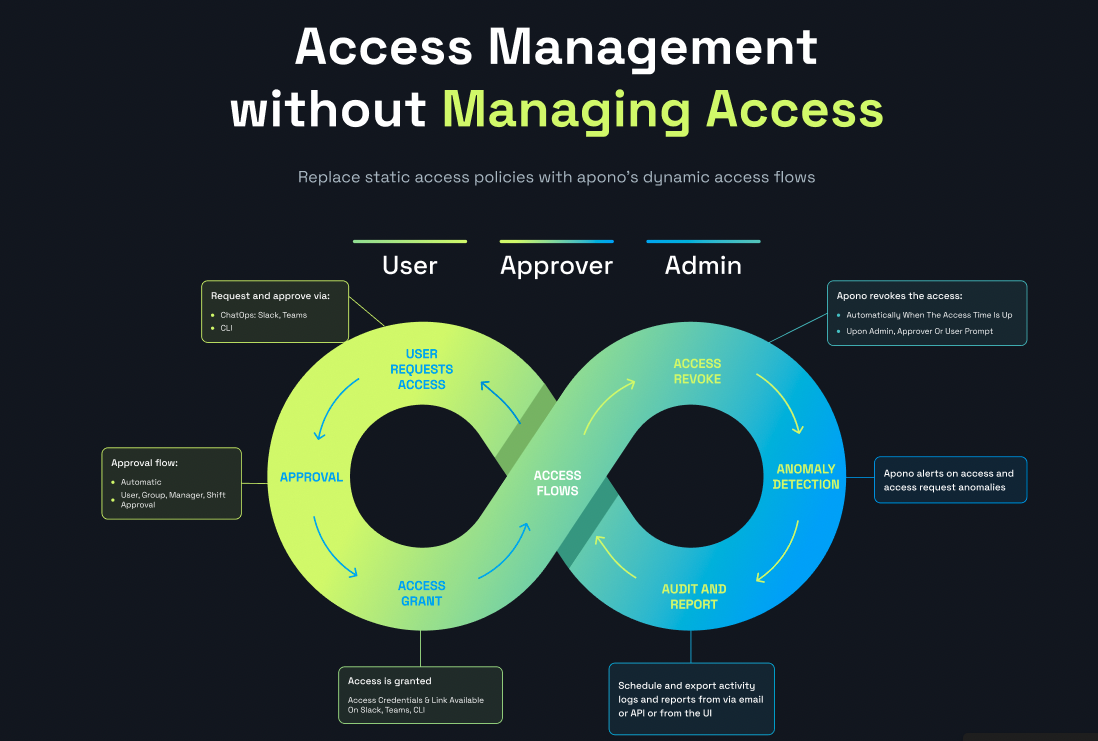
Apono helps **automate** this process as part of its access lifecycle:
## Benefits of working with Apono
### Automated grant & revoke
Apono helps automate the entire access lifecycle:
1. The admin defines the access lifetime per app, environment, resource and permission
2. The user requests access with Slack, Teams or CLI
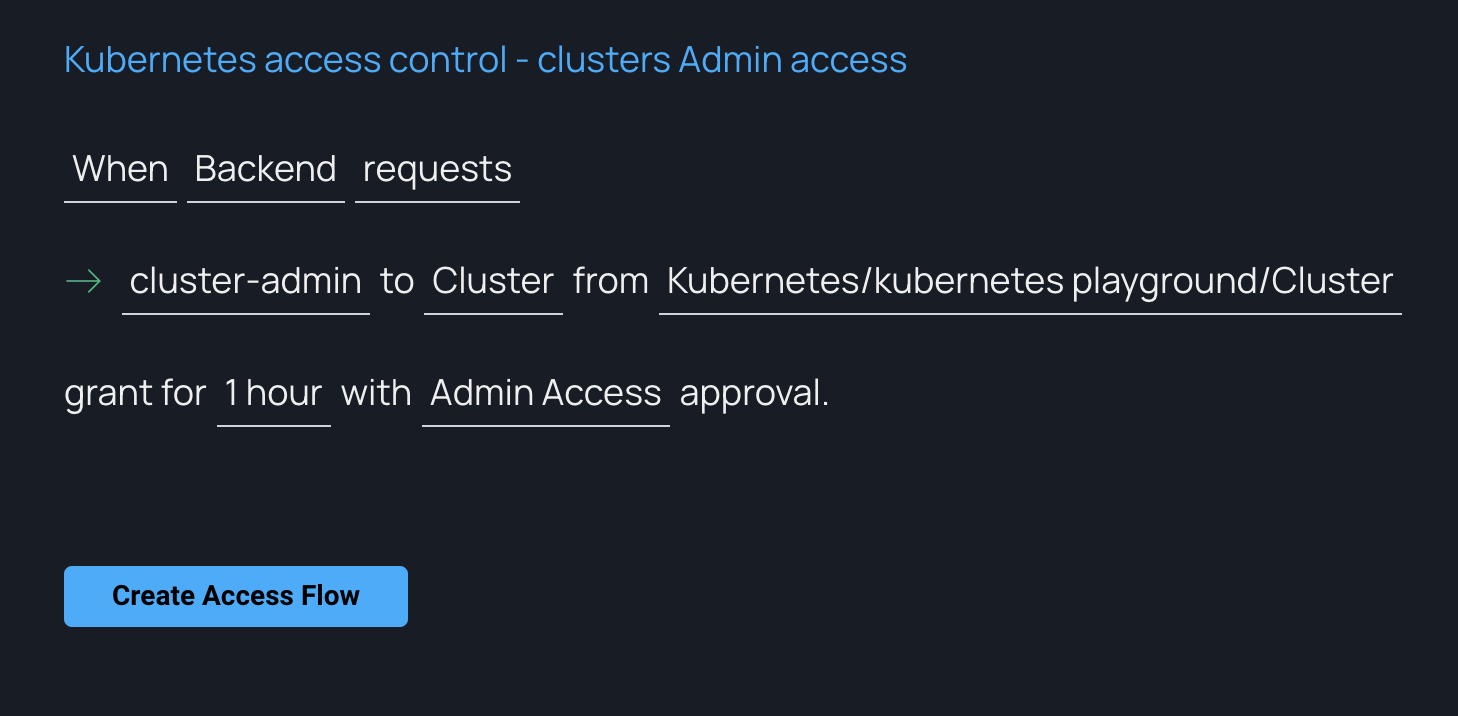
3. According to each [Access Flow](/docs/access-flows/access-flows.md), access is approved automatically or by approver(s)
4. When the access lifetime ends, Apono revokes the access for you automatically
5. All requests, approvals, grants and revocations are fully audited
{% hint style="success" %}
Congratulations! You just automated the complete access lifecycle, saving time and resources and reducing standing access
{% endhint %}
### Panic button
Apono serves as your central control tower for shut-down - in case of **emergency or incident**, you can revoke all active access directly from Apono:
1. Admins can use the Apono UI to find and revoke all active access\
2. Approvers (managers, resource owners, developers on duty, DevOps, DevSecOps, SRE, IAM Ops, CISO or anyone else you want) can revoke access
3. End users can revoke their own access
### Admin and approver control
With Apono, admins and approvers have full control over who can access what:
1. Admins can define Access Flows with automatic revocation
2. Admins can find all active access and revoke it
3. Approvers (managers, resource owners, developers on duty, DevOps, DevSecOps, SRE, IAM Ops, CISO or anyone else you want) can revoke all the active access they approved
### Access visibility
It's hard to keep track of all the active access in the organization. Access can be granted in the IdP for users and groups, users can be granted access directly from apps' IAM portals, using roles, permission sets or users (personal or shared).
This causes access drift, shadow admins, orphaned accounts, partial offboarding, and unused access which increases downtime and attack risks.
Apono lets you find out who has access to what in the organization:
**BEFORE**
Take standing access for users and groups and turn into dynamic, just-in-time, on-demand, temporary access. It's **dynamic, easy to manage and fully audited**.
**AFTER**
***
### Resolve stuck revocations
In rare cases, access requests may remain in the **Revoking** state when Apono attempts to revoke access and cannot reach the integration or connector. This can happen when the integration, connector, pod, cluster, or target environment is unavailable.
Follow these steps to resolve stuck revocations:
1. In your affected target environment, attempt to restore the affected integration or connector so Apono can complete the revocation.
{% hint style="info" %}
After connectivity is restored, Apono can continue the revocation process and remove access from the target environment.
If connectivity cannot be restored, continue to step **2**.
{% endhint %}
2. On the [**Activity**](https://app.apono.io/activity) page, from the **Status** filter, select **Revoking**. The **Mark as Canceled** button appears on the page.
3. Click **Mark as Canceled**. The **Mark as *****Revoke Canceled*** confirmation window appears.
{% hint style="warning" %}
Use **Mark as Canceled** only when you cannot restore the integration or connector and need to unblock integration deletion.
Canceling a revocation **does not** confirm that access has been removed from the target environment. The access may still be active. You must manually remove the access from the target environment.
{% endhint %}
4. After reviewing the confirmation window message, click **Mark As Canceled**. The pop-up window closes. The affected access requests (filtered in step **2**) change to **Revoke Canceled** status. This process might take a few minutes.
5. In the target environment, manually remove the user access to prevent standing access.
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://docs.apono.io/docs/access-flows/revoking-access.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.