Protecting PII and Customer Data
How to protect PII and keep customer data safe with Apono
Intro
PII protection is crucial. The two most common use cases for PII protection are:
Your company needs to comply with HIIPA, SOC 2, PCI DSS, GDPR or other compliance standards and regulations that require safeguarding Personal Identifiable Information.
To enable sales and client satisfaction, you need to put guardrails around customer data; they want to know access is highly restricted to their tenant and their data.
Apono is here help!
Read more about PII and why it's so important
How to protect PII with Apono
Apono specializes in protecting data. With Access Flows, you can control exactly who can access DBs with any permission (read, write, create, delete, duplicate, admin, and more):
We support all common databases and keep adding more:

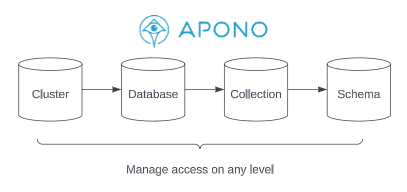
We help you manage access with full granularity and flexibility:
Apono can automate access management for clusters and databases, but also for collections and schemas
How it works
Integrate Apono with your data repository
Apono will auto-discover clusters, databases, collections and schemas
Create an Access Flow for the resource type you want to control
Fully auditable with logs and reports out-of-the-box
How to secure customer data with Apono
Database access control is key to customer satisfaction - customers want to (and are required to) ensure least privilege to their data and their customers' data by their vendors.
This may include metadata, like users, resource names (like DBs, repositories, etc.), DaaS (data as a service) titles and paths, and also actual data, especially Personal Identifiable Information of customers and employees (names, IDs, addresses, emails, phone numbers, and any other personal attribute).
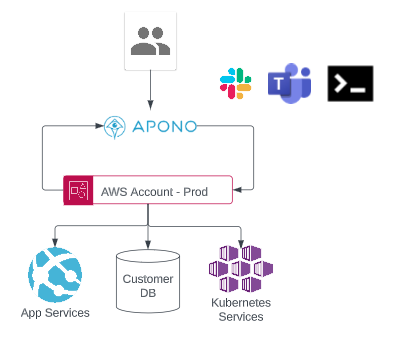
Apono handles the access workflow for each user who needs to access a customer environment, account, tenant or database, including approval, provisioning, secure access details, revocation and audit:
How it works
Put your customers at ease with Apono's documentation and architecture. Contact us and we'll provide out-of-the-box, white-labeled documentation!
Integrate Apono with your data repository
Apono will auto-discover clusters, databases, collections and schemas
Create an Access Flow for the resource type you want to control. Limit access using:
Tags for customers' resources
Specific environments or tenants
Specific customer databases
Users will be able to request access to perform any action (READ, WRITE, DELETE, ADMIN, etc.) on customer data
Last updated
Was this helpful?
