How to: Visualize Kubernetes Access
Integrate Kubernetes to get immediate visibility to your K8s permissions
How to: Visualize Kubernetes Access
Intro
How it works
Step 1: Sign up to Apono
Step 2: Connect a K8 Cluster
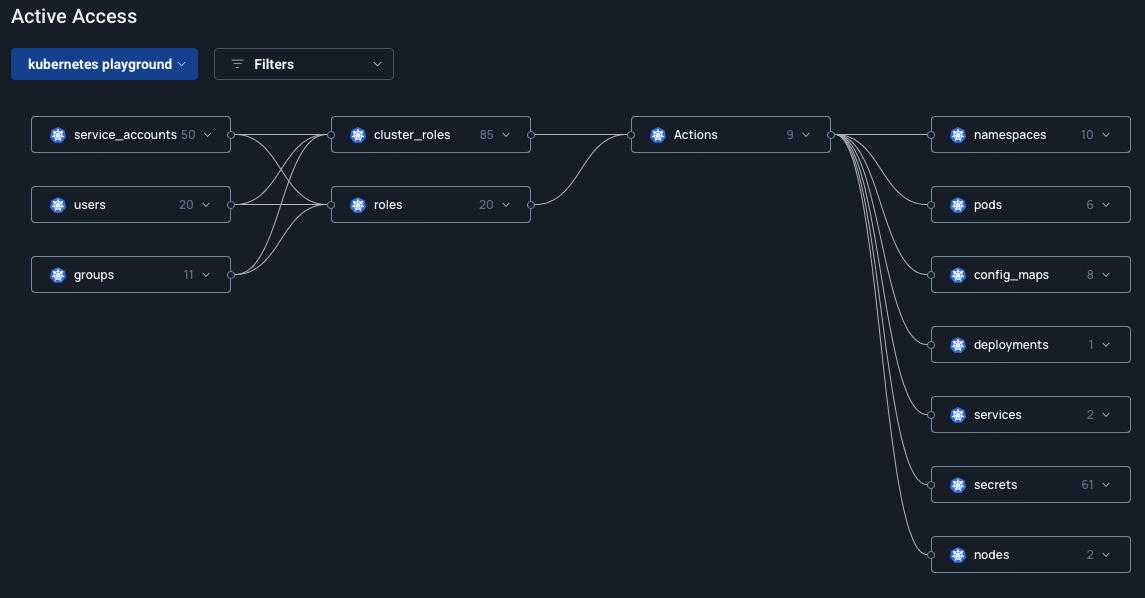
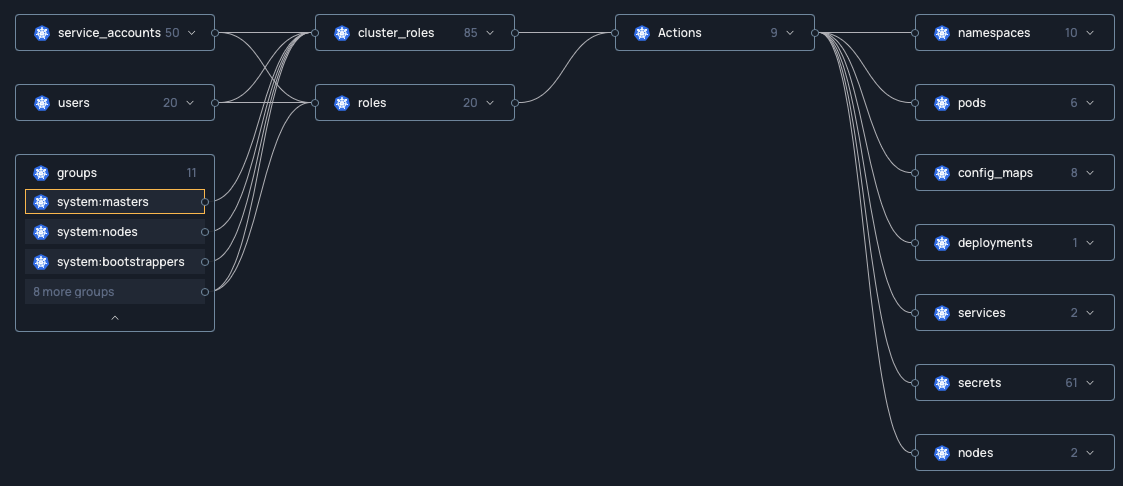
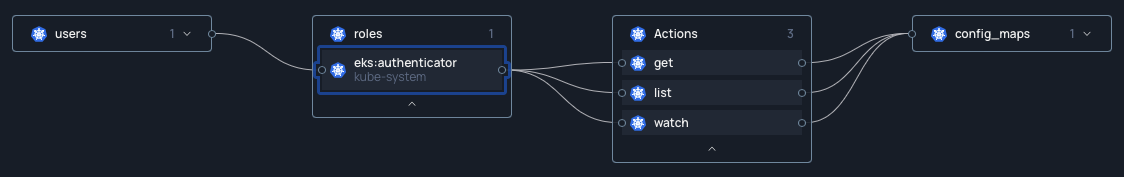
Step 3: Explore K8 access using the Apono Access Graph
Next steps
Last updated
Was this helpful?
